Shadow AI on corporate endpoints.
Claude Code, Copilot CLI, Cursor agents, custom LangChain workflows — they're already running on developer laptops and engineering VMs. Security has no inventory, no policy, and no kill switch.
DarkGuard is the runtime authority layer for AI agents and developer copilots running inside your organization. Every shell command, every script, every action — intercepted, classified, and authorized at the endpoint. In milliseconds.
Your developers and operators run AI agents that can read code, write files, call APIs and spawn shells. Most organizations have no way to see — let alone authorize — what those agents actually do at the endpoint.
Claude Code, Copilot CLI, Cursor agents, custom LangChain workflows — they're already running on developer laptops and engineering VMs. Security has no inventory, no policy, and no kill switch.
An AI agent calls bash or powershell.exe, the OS happily executes. There's no record of which prompt, which model, or which human is responsible — only that the file was deleted.
Today's options are blocking the tool entirely or trusting it blindly. Low-risk reads and high-risk writes get the same treatment, so teams either pull the agent or wave everything through.
NIS2, ISO 27001, the EU AI Act and ENS all demand traceable, runtime evidence of human oversight over consequential automated actions. Static policy documents don't satisfy any of them.
DarkGuard installs a lightweight agent on every machine where AI runs. Each command an AI tool tries to execute is intercepted, evaluated against your rules, and either allowed, denied, or escalated to a human operator — in milliseconds, with a full audit trail.
Every command an AI agent attempts is captured at the OS layer before it reaches the shell, the filesystem, or the network.
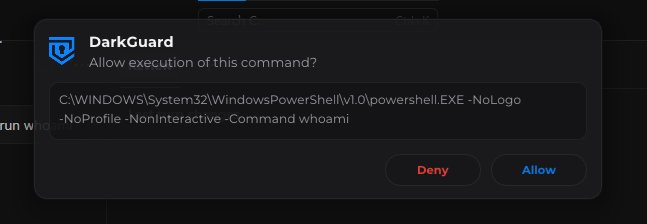
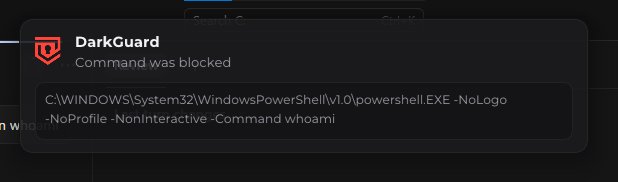
Allow trusted reads. Deny known-dangerous patterns. Escalate ambiguous actions to a named human, in real time.
Whitelisted actions clear in under 3 ms. Your developers don't notice DarkGuard until something actually matters.
One place to define, version and roll out command policies across every endpoint, organization and department.
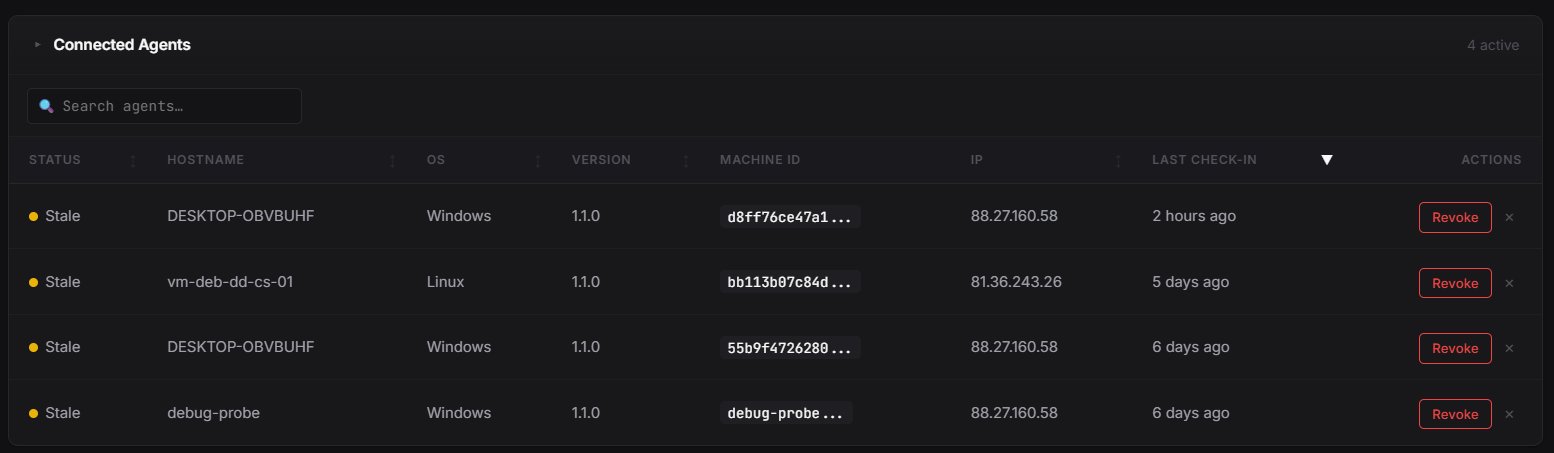
Every agent's status, last check-in and recent activity, in one console — across Windows, Linux and macOS.
Immutable logs of every command, every verdict, every human decision. Export-ready for auditors and regulators.
Watch how DarkGuard catches a Claude Code agent attempting destructive commands on a developer workstation, escalates the call to the SOC operator, and records the whole exchange.
Single binary on every endpoint where AI runs. Windows, Linux, macOS. MDM-friendly.
Allow, deny or ask — by command pattern, package, organization or department.
Every AI-issued command is routed through DarkGuard before it executes.
Generate auditor-ready evidence on demand, mapped to NIS2, ISO 27001, EU AI Act.
Designed by DARKDATA's incident response operators for the people who actually answer the phone when an AI does the wrong thing.
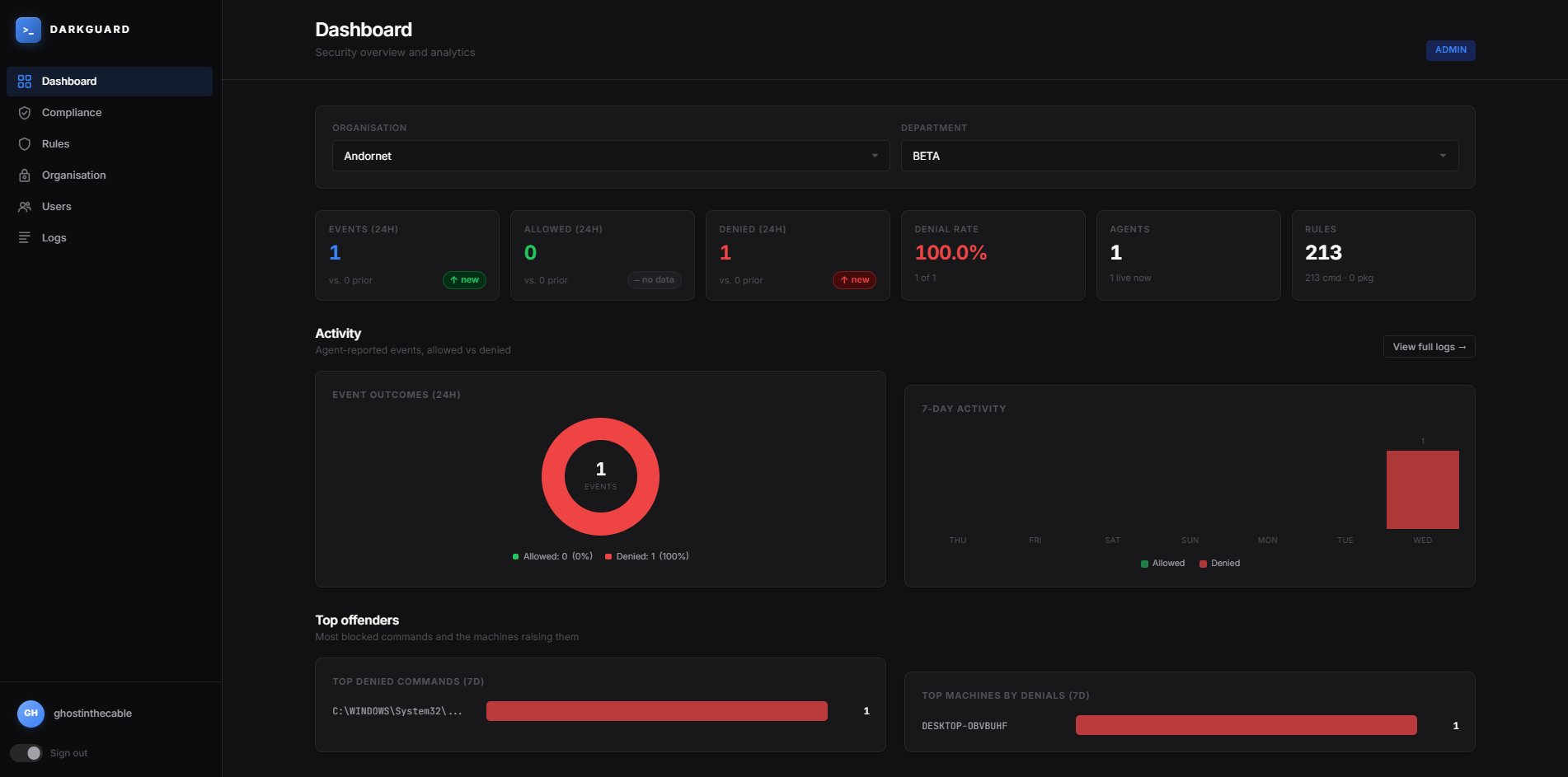
One pane of glass for events, denials, denial rates and the rules behind them. Filter by organization, department or endpoint.
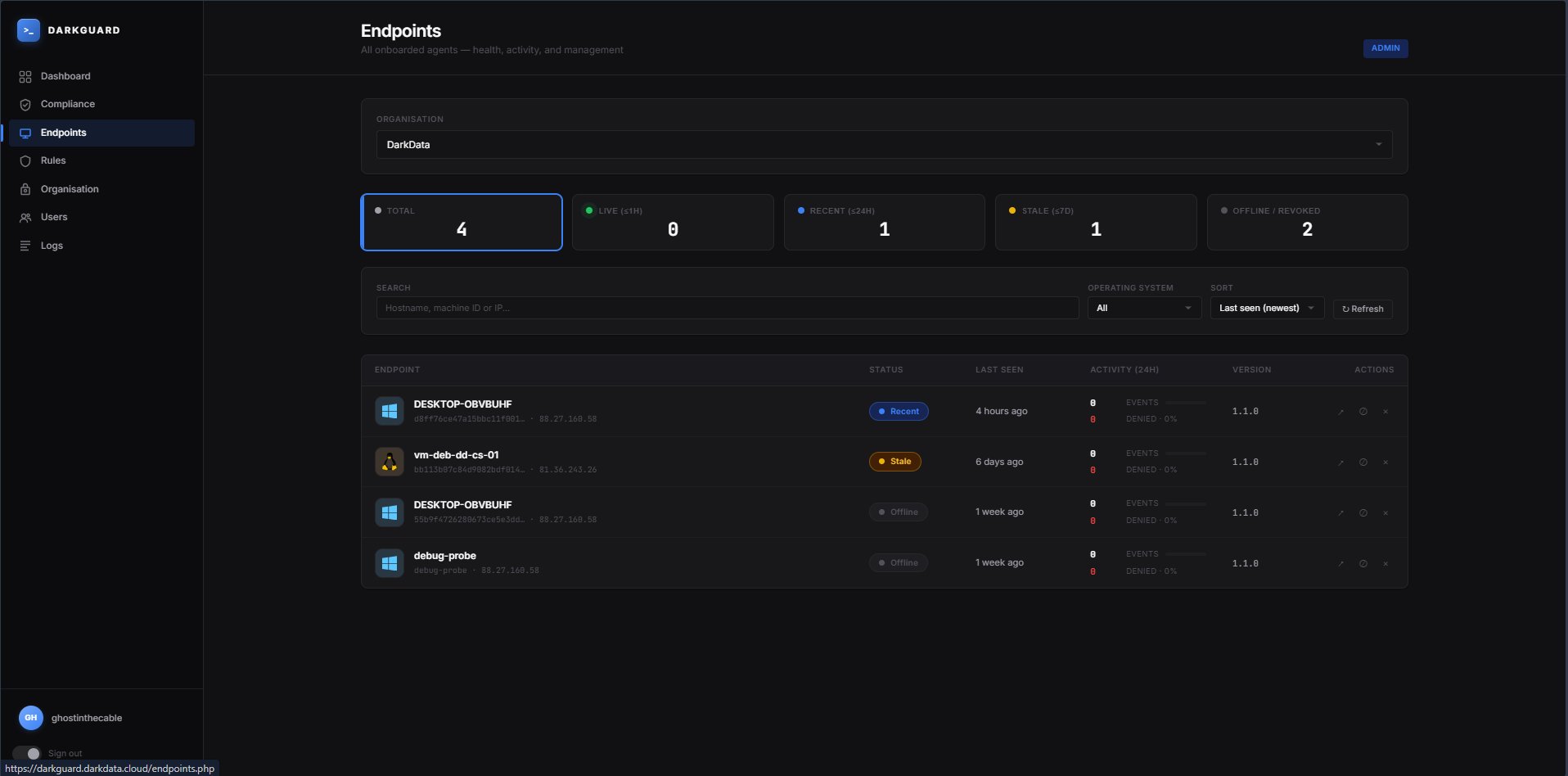
Every onboarded agent reports back continuously. Stale, offline or revoked endpoints are surfaced before they become a blind spot.
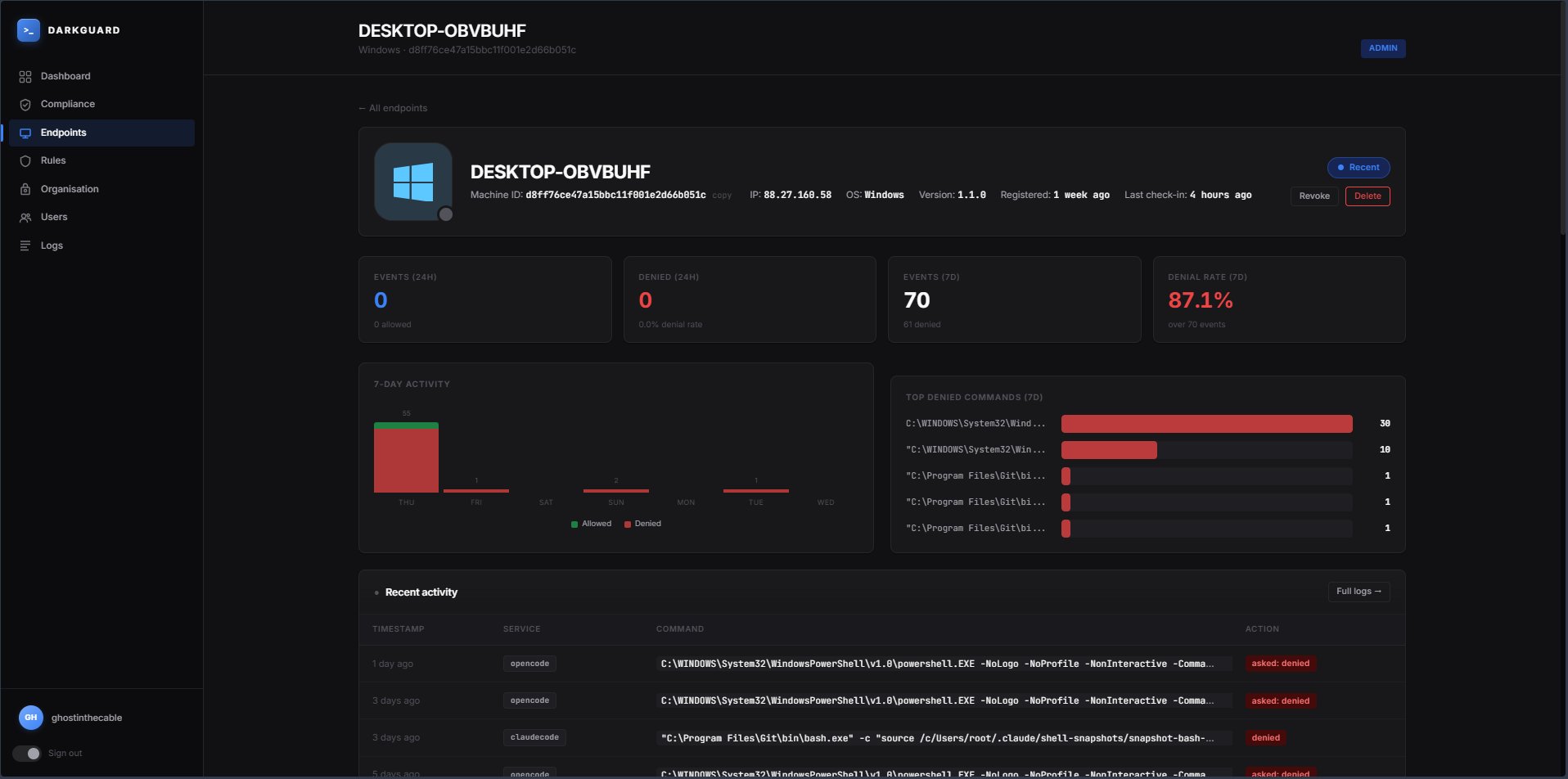
Drilldown into any endpoint to inspect denial rate, top denied commands and a full timeline of recent activity by service — Claude Code, OpenCode, custom agents.
Author rules with wildcards and pattern matching. Roll them out instantly across every endpoint in scope. Maintain separate rule sets per organization or per department.
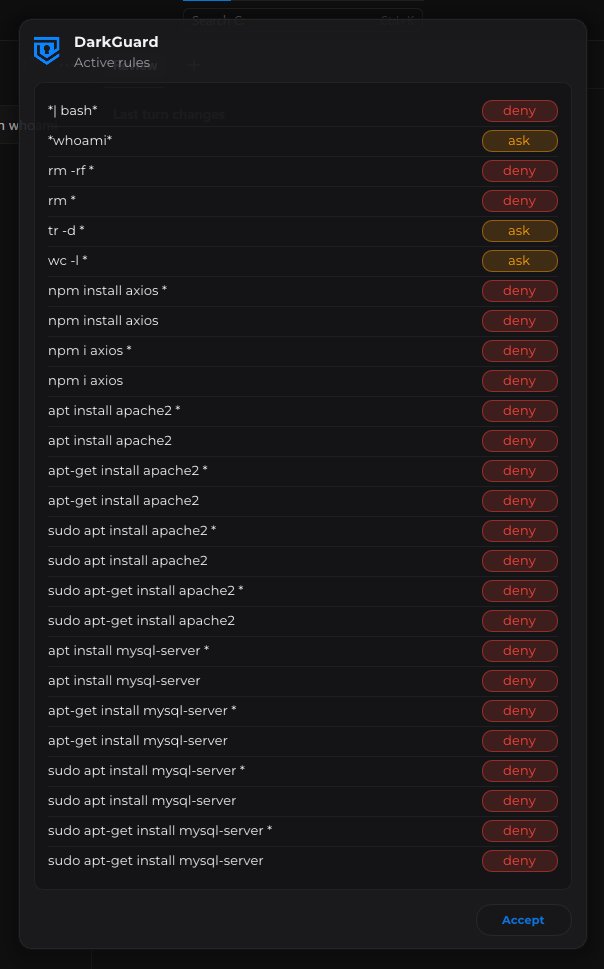
Ambiguous actions are escalated to the named human authority on duty — directly on their device. Approve in one click, deny in another, with the full command, host and AI context attached.
The same DarkGuard agent runs everywhere your engineers and operators run AI — corporate laptops, build servers, jump hosts, EC2 instances. Revoke any agent in a click.
DarkGuard ships with a built-in compliance posture — license health, rule coverage, agent liveness and governance — scored continuously and exportable on demand.
Mapped to the controls your auditors actually ask about, by the same operators that already deliver DFIR, SOC and CTI services to leading European cyber insurers.
AI agents aren't suggesting code anymore — they're running it. On laptops, on production servers, with your credentials, against your data. The infrastructure to govern them at runtime did not exist. Now it does.
And the vast majority of organizations have no inventory of which agents touch which endpoints, let alone what they've executed.
High-risk AI obligations require demonstrable runtime human oversight. Static documentation no longer satisfies the requirement.
Once an AI tool can call bash, the only meaningful control is at the command itself. That's exactly where DarkGuard sits.
One agent. One console. No vendor lock-in on which AI tool, model or framework your teams choose to use.
DarkGuard is agent-agnostic. If it can call a shell, write a file or hit a network endpoint, DarkGuard can authorize it.
Single-binary agent for every endpoint. Centralized, multi-tenant console. Your data, your environment, your call.
Tell us what your teams run and where, and we'll set up a private demo against a representative environment. A real human from DARKDATA will reply within one business day.